
View from the C-Suite: Made-to-measure makes its 'Mark' » Strategy
4.9
(114) ·
$ 0.50 ·
In stock
Description
Beyond File Search: A Novel Method - vulnerability database
Assess Your Risk From Ransomware Attacks, Powered by Qualys - vulnerability database
ACDH-2020/src/data/acdh/courses.json at master · br0ast/ACDH-2020 · GitHub

CAOT 32, Chapte 6 Revising Business Messages Business Communication: Process and Product, 8e Mary Ellen Guffey & Dana Loewy Flashcards

Blog, maXbox, maxbox
Russian Sandworm Hackers Impersonate Ukrainian Telecoms to D - vulnerability database
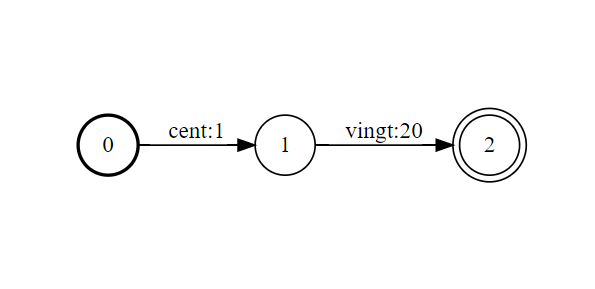
NeMo-text-processing/tutorials/WFST_Tutorial.ipynb at main · NVIDIA/NeMo-text-processing · GitHub

BUS 499 Week 8 Assignment 3.docx
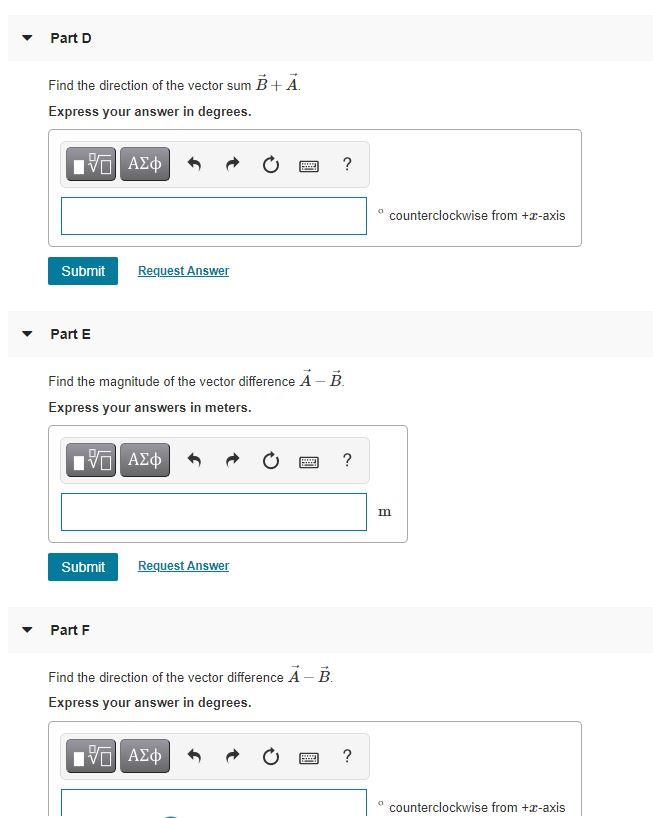
Solved You may want to review (Page) For related
Related products
You may also like
copyright © 2018-2024 erestandem.es all rights reserved.








